How to Design Secure Software Architecture
Designing secure software architecture is a vital part of any software development project. It is essential to ensure that the software is secure and can protect the data and resources of the organization from malicious attacks, unauthorized access, and other security threats. This article will provide an overview of the key principles of secure software architecture and discuss the steps involved in constructing a safe software architecture.
Secure software architecture design is a critical component of any software development endeavor. It is the process of constructing a system that is secure from malicious attacks and other security threats. This article will provide an overview of the fundamentals of secure software architecture design, including the principles of secure design, the elements of a secure system, and the steps involved in designing a secure system.
The principles of secure design are the foundation of any secure software architecture. These principles include the use of defense in depth, the principle of least privilege, and the principle of secure defaults. Defense in depth is the practice of using multiple layers of security to protect a system. The principle of least privilege requires that users and processes have only the minimum amount of access necessary to perform their tasks. The principle of secure defaults requires that all security settings are set to their most secure values.
The components of a secure system include authentication, authorization, encryption, and logging. Authentication is the process of verifying the identity of a user or process. Authorization is the process of granting access to resources based on the user’s identity. Encryption is the process of encoding data so that it can only be read by authorized users. Logging is the process of recording events and activities in a system.
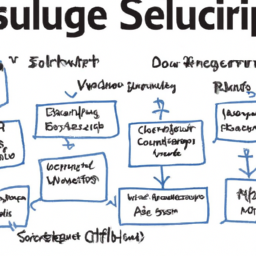
The steps involved in designing a secure system include identifying security requirements, designing the system architecture, implementing security controls, and testing the system. The first step is to identify the security requirements of the system. This includes identifying the types of threats that the system must be protected against, the types of data that must be protected, and the types of users that will be accessing the system. The next step is to design the system architecture. This includes designing the system components, the data flows, and the security controls. The third step is to implement the security controls. This includes implementing authentication, authorization, encryption, and logging. The final step is to test the system to ensure that it meets the security requirements.
Secure software architecture design is an essential part of any software development project. By following the principles of secure design, implementing the components of a secure system, and following the steps involved in designing a secure system, developers can ensure that their systems are secure from malicious attacks and other security threats.
Establishing a secure development process is essential for developing secure software architecture. This process should include a secure coding standard, secure coding guidelines, and a secure development life cycle. Secure coding techniques should be employed to guarantee that the software architecture is secure. This includes utilizing input validation, output encoding, and authentication and authorization. Authentication and authorization should be implemented to ensure only authorized users can access the software architecture. Strong passwords, two-factor authentication, and role-based access control should be used. Secure data storage should be used to guarantee that sensitive data is stored securely. This includes encryption, secure databases, and secure file systems. Secure communication protocols should also be used to ensure data is transmitted securely. This includes employing secure protocols such as SSL/TLS and IPSec. Secure coding frameworks should be used to guarantee that the software architecture is secure. This includes frameworks such as OWASP and SANS. The software architecture should also be monitored and tested regularly. This includes utilizing static and dynamic analysis tools, penetration testing, and vulnerability scanning. Secure deployment processes should also be used to make sure the software architecture is deployed securely. This includes using secure deployment tools and secure configuration management.
Secure software architecture is vital for any software system. It is essential to consider the security requirements of the system, the security threats that may be present, and the security measures that can be taken to protect the system. By following the best practices outlined in this article, software architects can design secure software architectures that are robust and resilient to attack. It is also important to stay up to date with the latest security trends and technologies to guarantee that the system remains secure.